Multi-Factor Authentication (MFA): Technical and Assurance Guide
1. Introduction
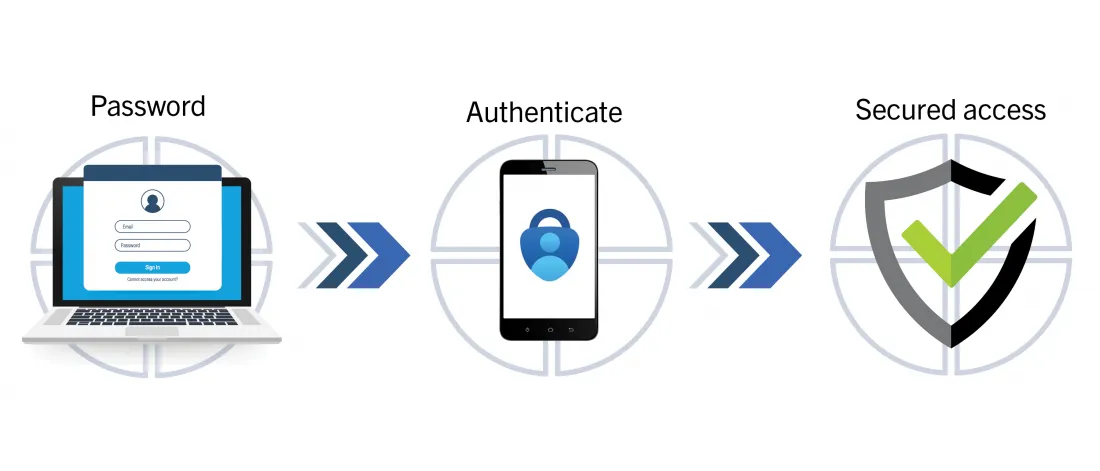
Multi-Factor Authentication (MFA) is a core security control for identity and access management. Its objective is to reduce account takeover risk by requiring independent authentication factors, rather than relying on a single credential.
From a security assurance perspective, MFA must be evaluated at two levels:
- Design adequacy: Are factor choices and flows appropriate for the risk level?
- Implementation robustness: Can the mechanism be bypassed, replayed, or abused?
This guide provides a professional test methodology for web and API environments.
2. MFA Control Model
MFA combines factors from distinct categories:
- Knowledge factor: password, PIN, or passphrase.
- Possession factor: authenticator app, hardware token, trusted device, or SMS channel.
- Inherence factor: biometric signal (fingerprint, face, voice).
Control strength depends on factor independence, enrollment integrity, and resistance to phishing, replay, and brute-force attempts.
3. MFA Architecture and Token Lifecycle
3.1 Typical implementation patterns
Common second-factor implementations include:
- TOTP (time-based one-time password)
- HOTP (counter-based one-time password)
- SMS OTP
- Push approval flows
- FIDO2/WebAuthn authenticators
3.2 Security-sensitive lifecycle stages
Each MFA deployment should be assessed across the full lifecycle:
- Enrollment and device binding
- Secret generation and storage
- Verification workflow and error handling
- Recovery and reset procedures
- Logging, monitoring, and incident response
4. Assessment Methodology
4.1 Scope and authorization
All testing activities must be explicitly authorized in writing and executed within a defined scope. Unauthorized testing is prohibited.
4.2 Data collection points
During assessment, analysts should inspect:
- Frontend code and exposed configuration
- API responses and authentication endpoints
- Session cookies and browser storage
- Backend logs and audit trails (when authorized)
4.3 Control objectives
At minimum, verification should cover:
- Correct factor enforcement for all login paths
- Resistance to OTP replay and race conditions
- Rate limiting and lockout behavior
- Secure transport and secret handling
- Recovery flow hardening (fallback controls)
5. Practical Testing Procedures
5.1 Tooling baseline
- Burp Suite for request/response inspection and replay analysis
- oathtool for TOTP validation
- curl for API-level verification
5.2 TOTP validation
# Install oathtool
sudo apt install oathtool
# Generate a TOTP code from a test secret
SECRET_KEY="JBSWY3DPEHPK3PXP"
oathtool --totp -b "$SECRET_KEY"
Assessment points:
- OTP validity window and clock drift tolerance
- Single-use enforcement
- Secret exposure in client-side data or responses
5.3 API and transport checks
# Example OTP verification request
curl -X POST https://example.com/verify-otp \
-H "Content-Type: application/json" \
-d '{"otp":"123456"}'
Assessment points:
- TLS-only transport for all authentication endpoints
- No OTP or secret leakage in verbose error responses
- Proper HTTP status code behavior and consistent failure messages
5.4 SMS OTP checks
SMS-based MFA should be reviewed for:
- Short validity period
- Strict attempt limits
- SIM-swap and channel interception risk mitigation
- Safe fallback logic when SMS delivery fails
5.5 Push approval checks
Push-based MFA should be reviewed for:
- Session binding (approval linked to the right login attempt)
- Prompt context clarity (device, geolocation, timestamp)
- Deny/timeout handling and fraud telemetry
6. Common Non-Conformities
Frequent weaknesses observed in MFA implementations:
- OTP reuse accepted by backend
- Missing or weak rate limiting
- Overly permissive recovery channels
- Secret material logged in plaintext
- Inconsistent MFA enforcement across mobile/web/API flows
Each finding should include technical evidence, exploitability assessment, and remediation priority.
7. Professional Implementation Requirements
Recommended baseline requirements:
- OTP lifetime: short and risk-appropriate.
- Replay protection: enforce one-time semantics.
- Rate limiting: adaptive controls with lockout thresholds.
- Secure storage: protect seeds, tokens, and recovery artifacts.
- Monitoring: detect anomalous MFA activity patterns.
- User experience safeguards: clear prompts and secure recovery.
8. Reporting and Evidence
A professional MFA assessment report should document:
- Scope, assumptions, and test constraints
- Methodology and tooling
- Verified controls and failed controls
- Reproducible evidence (requests, responses, logs, screenshots)
- Risk rating and remediation guidance
This evidence-first approach improves technical traceability and supports governance, audit, and compliance workflows.
9. Conclusion
MFA is not only a login feature; it is a critical control in the broader security posture of an application. A robust implementation requires secure design, strict verification logic, resilient recovery procedures, and continuous monitoring.
When assessed with a structured and evidence-driven methodology, MFA significantly improves resistance to credential compromise and account takeover.